After Mirai: The new IoT scare ‘Reaper’ and what we can do about it

Remember last year in September? Remember when the Internet suffered a major DDoS attack? That was Mirai. An IoT malware designed to infect thousands of unprotected IoT devices and carry out a large scale attack on the internet. Last year we asked in this blog, if Mirai was just the beginning. Seems we were right. According to security specialists, we have to embrace for worse things to come. ‘Reaper’ is the new scare. But we’re not lost. We all could do something about it. As well as consumers and especially as manufacturers of IoT devices.
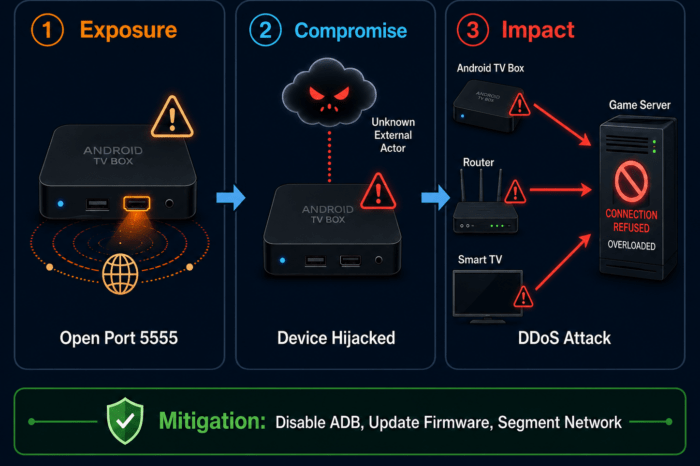
According to Brian Krebs, US-based investigative Journalist and IT security specialist, something bad is brewing on the IoT horizon. After last years “Mirai” attack that took over thousands of IoT devices and carried out successful Distributed Denial of Service (DDoS) attacks on various websites and online services, a more powerful malware seems to be just around the corner. ‘Reaper’ or ‘IoTroop’ are the new, far more advanced strains of a malware that might take over control soon using a massive botnet of infected devices.
According to Krebs, they might even be so powerful, they could cause widespread Internet disruption. Krebs warns: Reaper might not solely have DDoS attacks in mind. With millions of infiltrated IoT-devices worldwide it could be used for many purposes. Reaper could be a malware, that does not even intend to draw much of attention. It could also be used to secretly hijack IoT devices and use them as proxies to assist masking criminal online activities. Or in a different scenario, to build up a network of infected devices that could serve criminals “as jumping-off points for exploring and exploiting other devices”.
Users probably wouldn’t even find out that their devices were being hacked. And there lies the danger: If you’re not aware that your device is doing something it shouldn’t do, you probably don’t bother much about securing your IT enviroment. While you think that everything is fine, it is actually not.
Reaper focuses on wireless IP cameras – for now
So far, Reaper has not carried out any attacks on the net. However, we shouldn’t wait until it happens. Unlike Mirai, that used weak password cracking, Reaper infects IoT devices by exploiting multiple IoT device vulnerabilities, mainly on wireless IP cameras. So as a user it’s mandatory to keep your network and IoT devices up-to-date. Security specialists at Netlab 360 identified several IoT vulnerability exploits integrated in the malware so far and published a list of affected vendors.
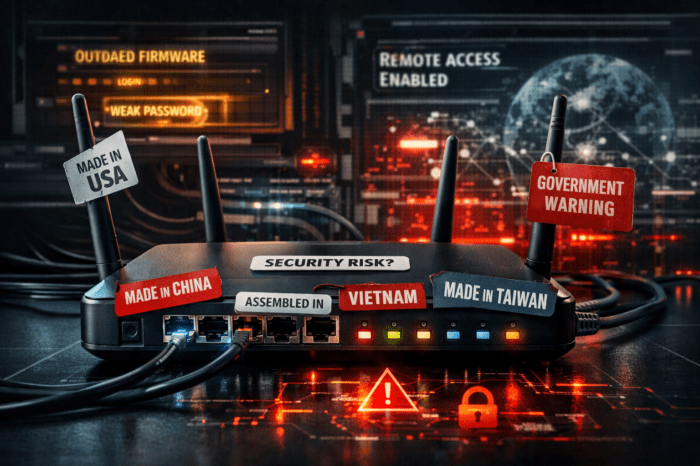
As a great weakness in the design of IoT devices Krebs mentions the inclusion of so called peer-to-peer (P2P) networking capabilities that are being implemented in countless security cameras, digital video recorders (DVRs) and various other gear. The weakness here: attackers could remotely locate and gain access to systems that otherwise are not even directly connected to the internet but via a cloud-platform which leads consumers to live under the illusion their systems are safe. Krebs even suggests not to use any hardware that advertises P2P functionality.
Manufacturers need easy remote maintenance
Keeping the Internet safe is a constant arms race. New technologies bring new vulnerabilities. Consumers should not install and forget. Keeping systems constantly up-to-date is mandatory.
But it’s also the duty (and challenge) of manufacturers to keep their devices easy to use but hard to hack. Unfortunately, many still tend to avoid a product design that allows painless over-the-air updates like consumers know it from smartphones or TV Set-Top-Boxes. But what is common there, should be common on every IoT device.
However, since many IoT devices are constrained in abilities and power consumption, that may sound like a difficult task. Not necessarily.
To make that possible, the devices firmware needs to offer a flexible framework that allows easy remote maintenance: Delivering updates „just-in-time” to clients is one thing. However, updating the devices over the air – without draining battery and without any manual intervention on the user side – is the safer solution. It’s in the consumers own interest, that his devices are always prepared for new threats with state of the art technology.
If all manufactures would design their products in a matter so they can be updated automatically while in service, the internet could become a lot safer place.
You may also like:
The Internet of Things under attack: Was Mirai just the beginning?