Was Russia working on its own IoT botnet?
Now published evidence suggests that the Russian secret service FSB wanted to develop its own botnet in the slipstream of the Mirai botnet, which was responsible for the failure of numerous Internet services in 2016, in order to specifically infect devices on the Internet of Things. Mainly the botnet, called “Fronton”, was supposed to attack webcams and digital video recorders. This is reported by various security portals online with reference to BBC Russia.
For example, the Russian hacker group “Digital Revolution” published numerous documents which indicate that Russia’s Federal Security Service (FSB) was working or perhaps still working on building its own botnet. The hacker group claims to have obtained the documents via a hack at a contractual partner of the FSP. The aim of the botnet was mainly smaller devices on the Internet of Things, which were to be infected with malicious code and brought under control. According to these documents, the FSB started planning the project as early as the end of 2016, shortly after the Mirai botnet paralysed numerous Internet services with millions of DDos attacks.
https://twitter.com/D1G1R3V/status/1240226232102539267
The documents should show a procurement order from the FSB Information Security Centre addressed to the InformInvestGroup CJSC. A Russian company that has worked with FSB on several occasions. As reported by BBC Russia and also ZDNET, the order was then passed on to a Moscow software company called ODT (Oday) LLC, which was hacked by Digital Revolution in April 2019.
Focus set on cameras and digital video recorders
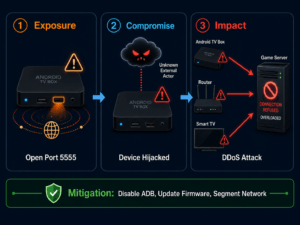
The time stamps of the documents indicate that the project was put together in 2017 and 2018. There are repeated references to Mirai. For example, it is suggested there that a very similar botnet be set up and made available to FSB. Dictionary attacks should be used to crack the passwords of IoT devices. According to Fronton’s specifications, surveillance cameras and digital recording devices were targeted, but not only. Devices that are connected to the Internet millions of times worldwide and unfortunately often belong to the weakest protected devices. Often these devices are equipped with standard passwords or are otherwise provided with weak passwords by their users.
High bandwidth tempting for attackers
However, the attack is not so much about tapping the cameras and spying on the collected footage, but about using the broadband capability of the devices to attack other servers. Since cameras have to transmit video data, they are usually very well connected to the Internet at high data rates. This is exactly what attackers then use to carry out targeted DDoS attacks with these “powerful” data centrifuges. The botnet itself should be controlled via a web-based interface, the location of the server being disguised behind a network of VPN and proxy servers. If the project were realized, the FSB could launch attacks on servers of its choice worldwide and paralyze infrastructures at the push of a button.