FCC Router Import Ban: Security Measure or Industrial Policy?
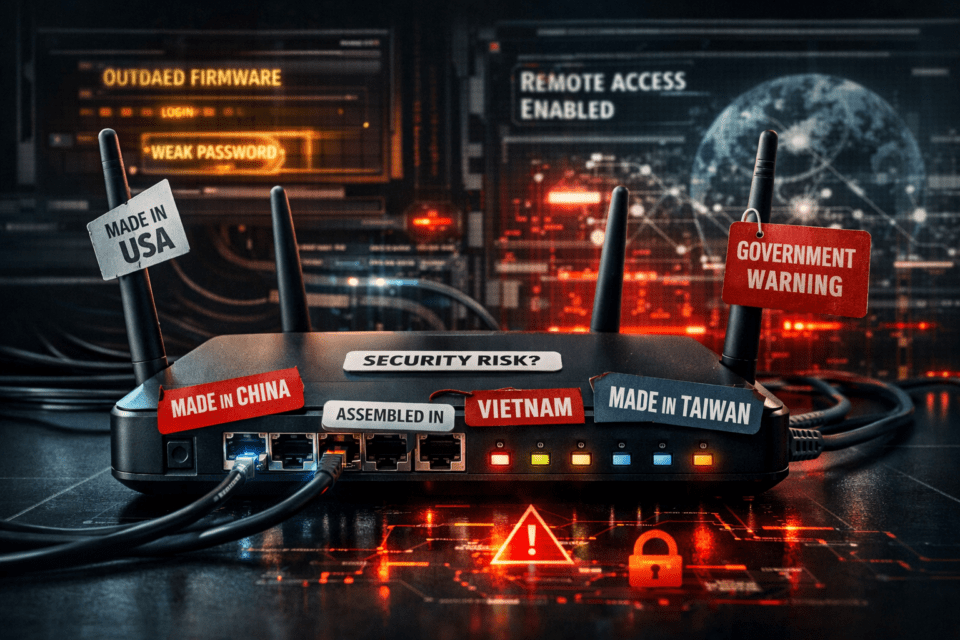
The FCC has banned the import of new foreign-made consumer routers – officially in the name of national security. But a closer look reveals the measure targets the wrong problem. And for IoT users, little changes for now – until the next router replacement is due.
The Key Facts at a Glance
- On March 23, 2026, the FCC added all foreign-produced consumer routers to its national security ban list – new models can no longer be imported or sold in the U.S. without special government approval.
- The only practical exception is Starlink, whose routers are assembled in Texas – but built with components from Taiwan, Vietnam, and Europe, which undermines the FCC’s own security logic.
- Security experts are unconvinced: router compromises happen because of missing updates and poor configuration, not because of where a device was manufactured – as recent botnets like KadNap and Chinese hacking group attacks on Cisco hardware make clear.
What the FCC Has Decided
On March 23, 2026, the Federal Communications Commission (FCC) – the U.S. regulatory authority for telecommunications – updated its so-called “Covered List.” This list identifies devices and services deemed to pose an unacceptable risk to national infrastructure. The newest addition: all consumer routers produced outside the United States. New models will no longer receive FCC authorization and may neither be imported nor sold in the U.S.
Existing devices are exempt – anyone who already owns a router may continue using it. Previously authorized models can still be sold by retailers until stocks run out. The ban applies exclusively to new device authorizations from the cutoff date onward.
Critically, the FCC defines “production” broadly. According to the agency’s official FAQ, every major stage of the production process counts – not just assembly, but also design and development. This means that even American brands like Netgear, Google Nest, or Amazon’s Eero fall under the ban if key stages of their production occur abroad.
For IoT users, this matters in a specific way: consumer routers function as the gateway for every device on a home network. Whoever controls the router potentially controls everything behind it – from smartphones to smart home devices to connected appliances.
The Official Justification
The FCC’s decision is based on an assessment by a White House-convened interagency body. Foreign-produced routers, the determination states, introduce supply chain vulnerabilities and serve as attack vectors for state-sponsored hacking groups. Specifically named are the Chinese groups Volt, Salt, and Flax Typhoon, which have exploited router vulnerabilities to attack U.S. infrastructure in recent years. According to Reuters, China controls around 60 percent of the consumer router market – making the implicit target of the measure clear, even though the rule formally covers all foreign production.
Particularly in focus is TP-Link, one of the world’s largest router manufacturers. The company was founded in China, has since relocated its headquarters to Irvine, California, and now produces primarily in Vietnam. U.S. government investigations into TP-Link over alleged ties to Chinese authorities have been ongoing since 2024.
The Starlink Contradiction
The only provider practically exempt from the rule is Starlink, SpaceX’s satellite internet service – because its routers are assembled in Bastrop, Texas. But this exception contains a fundamental contradiction: Starlink sources its chips in part from STMicroelectronics, a European-American semiconductor manufacturer, along with components from Taiwan and Vietnam. The assembly happens in the U.S. – the supply chain does not.
According to the FCC FAQ, U.S. assembly is sufficient for an exemption, provided the manufacturer offers “sufficient evidence” that assembly actually took place domestically. But anyone who cites supply chain security as the primary goal can hardly accept the assembly location as the sole criterion – while chips, circuit boards, and components continue to flow from the same countries elsewhere labeled as security risks.
What Security Experts Say
Skepticism among experts is widespread. Jason Soroko, Senior Fellow at certificate management specialist Sectigo, puts the core problem bluntly in a Dark Reading analysis: “Threat actors exploit these vulnerabilities across domestic and international hardware alike. By fixating on silicon origin rather than maintenance rigor, the directive risks misdiagnosing the disease, conflating supply chain provenance with the far more pervasive threat of administrative complacency.”
The point is well illustrated by concrete examples. Salt Typhoon – one of the Chinese hacking groups the FCC explicitly cites – exploited vulnerabilities in routers made by Cisco, a U.S. manufacturer, during its attacks on American infrastructure.
The KadNap botnet, which WeSpeakIoT covered in detail today, makes the same point even more clearly: over 14,000 routers were hijacked – predominantly devices made by Taiwanese manufacturer Asus. The attack did not exploit the devices’ country of origin. It exploited unpatched vulnerabilities in the AiCloud remote access feature and management interfaces that users had simply never disabled. The manufacturing location was irrelevant. What mattered was that nobody had updated the firmware.
Also telling is what the FCC’s conditional approval process actually requires from manufacturers seeking an exemption: a detailed plan to establish or expand U.S. manufacturing. Not a plan to make devices more secure.
Market Impact and Practical Consequences
Industry reactions are predictably mixed. Netgear, headquartered in the U.S., welcomes the ban and highlights its history of security-first design. TP-Link takes a pragmatic stance: since virtually all manufacturers are affected equally, the entire industry’s supply chains will now face scrutiny – which the company views as a positive step. Asus states that its existing product portfolio is unaffected.
For consumers, the practical implications are straightforward: anyone considering a router upgrade should act sooner rather than later. Once existing authorized stock is depleted, supply is likely to tighten and prices may rise. Drawing on the comparable drone ban from December 2025, the wait for first manufacturers to receive Conditional Approval – an official exemption permit – is likely around three months. As of now, no router manufacturer has received one.
Conclusion
The router is the centerpiece of every connected home – and a genuinely attractive attack target. In that sense, the FCC’s concern is understandable. But the chosen measure targets the wrong problem. Neither Salt Typhoon nor KadNap attacked devices because they were manufactured in China or Taiwan. They attacked devices that nobody had maintained.
What would actually help: mandatory security standards for all routers regardless of origin, automatic firmware updates as a default feature, and an end to the practice of shipping devices without ongoing update support. Instead, the FCC’s approval process demands a factory relocation plan – but no security improvement plan.
The measure could even backfire: less competition, higher prices, and a frozen market are poor conditions for better security. The country of origin of a router protects nobody from an attacker exploiting an unpatched vulnerability.













