Cyber Resilience Act: EU tightens the thumbscrews on IT developers

There is mixed feedback on the “Cyber Resilience Act” (CRA) now published by the European Union, which prescribes stricter rules for IT software and hardware manufacturers regarding the security of their products. While some welcome long-needed cybersecurity compliance rules, others complain of increased bureaucracy.
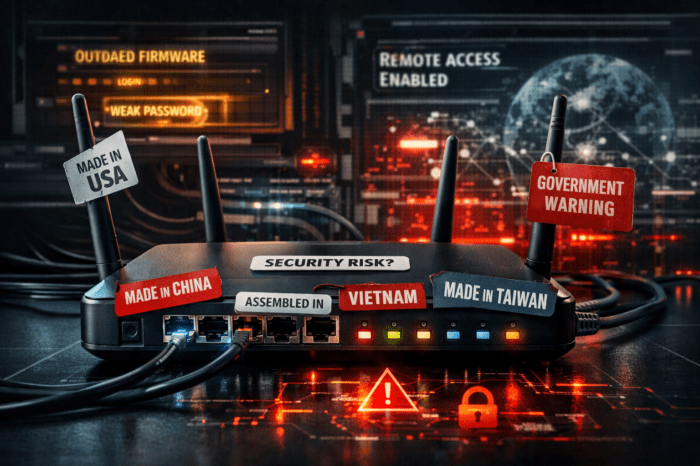
The Cyber Resilience Act has clear goals: On the one hand, the EU is extensively connected with a multitude of digital products in everyday life; on the other hand, cyberattacks continue to increase. Thus, the EU complains about an often low security level of many products, which is reflected in widespread vulnerabilities and the insufficient provision of corresponding security updates. Another factor complained of was insufficient understanding and access to information on the part of users, which prevents them from selecting products with adequate cybersecurity or using them in a secure manner.
“We need to be confident that products offered in the single market are safe,” said Margrethe Vestager, who is in charge of the “A Europe for the Digital Age”-portfolio. “Similar to how the CE seal on toys or refrigerators certifies safety, the Cyber Resilience Act ensures that the networked hardware and software products on offer meet strict cybersecurity requirements. To that end, we hold those who place the products on the market accountable.”
“Security doesn’t provide a direct return on investment, it just costs. With no discernible return. Until it goes bang,” Arron Finnon
Who is affected by the Cyber Resilience Act?
With the draft Cyber Resilience Act, the EU Commission is for the first time formulating binding Europe-wide security requirements for manufacturers and providers of “products with digital elements.” The document covers hardware and software that come onto the market both as end products or only as components. In the future, manufacturers will have to take digital security into account as early as the product development stage and fix any vulnerabilities that arise during the product’s lifetime and provide appropriate security updates for them.
“We must be able to rely on the fact that the products offered in the single market are secure,” Margrethe Vestager
TÜV Verband e.V. praises and criticizes
According to the Commission’s proposal, products are to be divided into different risk classes. However, many products with increased risk (“critical products” according to Annex III, Class 1) are also to be allowed to be placed on the market as a rule on the basis of a pure manufacturer’s self-declaration.
The TÜV-Verband e.V., which represents the political interests of the TÜV testing organizations, considers this approach to be misguided. It is not suitable for ensuring the necessary level of cyber security for networked products. According to the association, the consistent involvement of independent testing bodies for critical products is imperative in order to create the necessary trust in the security of digital technologies.
On the other hand, the association praises the fact that the EU Commission’s draft regulation takes into account the entire product lifecycle of a digital product and provides for corresponding security requirements for its service life. For example, necessary security updates are to be provided over a period of up to five years in the future. This will enable products to be used for longer and conserve resources.
Bitkom criticizes too short implementation period
Germanies digital industry association Bitkom generally praises the EU proposal. “The Cyber Resilience Act comes at exactly the right time,” commented Bitkom President Achim Berg. “Europe needs to focus more on defending against cyber attacks. The Cyber Resilience Act can make an important contribution to strengthening the security of networked devices.”
Bitkom is critical, however, of the implementation period of 24 months after coming into effect. In view of the significantly longer development cycles, this would present many companies with major challenges. It is therefore all the more important to keep the additional compliance costs that the Cyber Resilience Act will impose on companies to a minimum, he said.
Every 11 seconds someone falls victim of a security attack
The need for stricter rules when it comes to compliance with security measures in the development of hardware and software is also shown by the EU Science Hub’s report “Cybersecurity – our digital anchor – a European perspective.” According to the report, every 11 seconds an organization worldwide falls victim to a ransomware attack. Damage from the attacks is estimated to be €5.5 trillion in 2021, according to the report.
“We need a stronger security culture”.
More security in IT is also a long-standing demand of many experts. In an interview with WespeakIoT, Arron Finnon, Chief Technology Officer of Vindler GmbH, a consulting firm specializing in IT security, also criticized the often negligent approach to security taken by many IT companies. “Security is a cost factor that brings no direct return on investment, but only costs. Without any discernible profit. Until it goes bang,” he explained the common reason for the negligence.