How Your Business Can Prepare for the Risks of Reliance on IIoT

The internet of things (IoT) and industrial internet of things (IIoT) have become incredibly popular with consumers and many commercial and industrial operations. By 2025, an estimated 75 billion internet-enabled devices will be online. But for every one of those devices, the IoT security risks increase exponentially. What’s more, industrial IoT security is a huge concern, especially in utilities and infrastructure, where a hardware or software vulnerability could result in dangerous repercussions. Imagine the power grid going down all at once, or a city’s water supply being poisoned remotely.
Security cannot be an afterthought, and it cannot be something that’s only handled or maintained after adoption. From the moment you consider implementing IIoT and connected devices within your facility, you also need to start thinking about cybersecurity. Here are some ways to prepare your business for the impending reliance on IIoT and its accompanying risks.
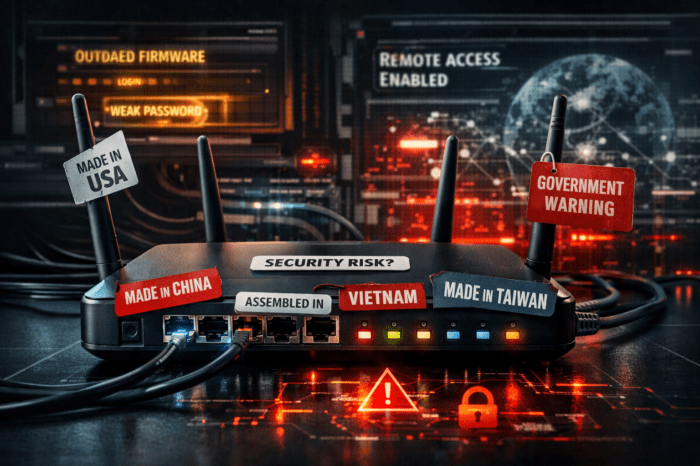
1. Get Your Network(s) in Order
At the heart of IIoT is data, and your network plays a huge role in how that data is processed and handled, especially when it comes to security. Before installing any internet-enabled devices within your facility, you’ll need to do a security audit on its local network. Is data encryption used, and is the connection secure? How is authentication handled, and are you using identity and access management tools to vet active users? Who else can access the network? What do your firewalls and security tools look like?
It’s also a good idea to establish a separate network specifically for IoT devices to keep it free from regular traffic. This prevents snooping and common IoT security risks while ensuring reliable performance. Depending on how you plan to implement the technology, you may even need to adapt your current networks. For example, environmental monitoring IoT sensors placed outside, in select locations, will need access to a reliable wireless network.
2. Strengthen Your Cybersecurity Team
An important distinction to make is that you don’t necessarily have to hire or supply an internal cybersecurity crew. Some third-party providers will offer support and they often have more resources available to lock down and monitor a network.
Regardless, before deploying IoT, organizations must have a proper security team in place. They should be fully educated on the latest security tools and practices, and it’s probably best to find professionals with direct experience in the field. Many operations roll out brand-new internet-connected devices and technologies without a proper team in place to monitor their use and safety. The risk isn’t always immediately apparent, but not having the right talent makes organizations vulnerable in many ways.
3. Build Awareness
Understand how the technology works and the risks that come along with it. Make sure everyone on the team and within the facility understands the ins and outs, too. Anyone interacting with the technology should know what role they play and what they can do to maintain security — like not sharing passwords, or never accessing systems outside of the designated terminals.
A 2014 U.S. state of cybercrime survey revealed that 42% of respondents said the security awareness training of new employees helped deter attacks. Team members should also spend time learning:
- Critical threat vectors
- Major cybersecurity attacks in your industry and how they played out
- Legal and regulatory compliance
- Automation tools to enhance and empower cybersecurity initiatives
- External security considerations like removable drives and remote access
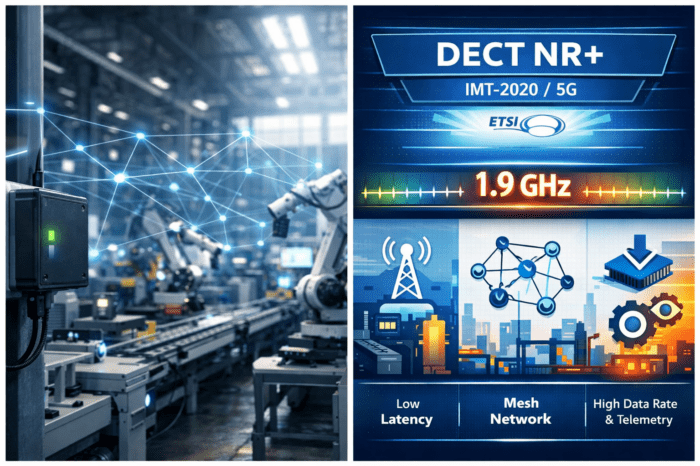
Understanding how IoT can and will be deployed is another major recommendation. Solutions may include smart sensors, retrofitted connectivity for legacy hardware, data collection tools, and contextual modifiers to provide insights and inform decision-making. The internet of things isn’t just about smart voice assistants and touchscreen devices that can access the internet anymore.
4. Deploy and Revise
As much as an organization’s leadership would love to roll out new technologies in one maneuver, that’s not ideal for security. When deploying IoT and related technologies, it’s critical to do so intermittently. This provides ample time to monitor the current iterations, improve security, ensure its reliability, and then move on. If it’s adopted all at once throughout the entire facility, employees may soon be overwhelmed with the logistics of ensuring security measures are working as expected.
Choose more specific use-cases to trial the technologies and roll them out one by one, making sure to test, assess, and revamp security policies and procedures until you’re satisfied with what’s available.
Ultimately, identifying and shoring up potential IoT security risks is just step one. Beyond that, you’ll need to have a team and platform in place to continue monitoring the network, connected devices, and active users. You’ll also need a proper security plan in place for when a breach or attack happens, so there’s a script for your teams that explains what to do.
Safety Starts With Vigilance
Industrial IoT security shouldn’t be an afterthought, and it doesn’t need to be intimidating. These essentials will help ensure organizations don’t get caught off-guard by the potential risks of new technologies, and help them focus on getting the greatest value out of the investment instead.