KadNap: How Hijacked Routers Become Tools for Cybercriminals

A new malware called KadNap has hijacked over 14,000 routers and turned them into a criminal proxy network. What makes the technology behind it particularly insidious, and why the problem extends far beyond home networks.
Key Takeaways
- KadNap uses a customized version of the decentralized Kademlia protocol to conceal its command infrastructure — making this botnet significantly harder to disrupt than classically centralized malware networks.
- Infected routers are rented out to cybercriminals via the proxy service Doppelgänger, who use them for DDoS attacks, credential stuffing, and targeted exploitation campaigns.
- No Asus-specific statement addressing KadNap has been published to date; security researchers recommend an immediate firmware update, factory reset, and disabling unused services such as AiCloud and remote management.
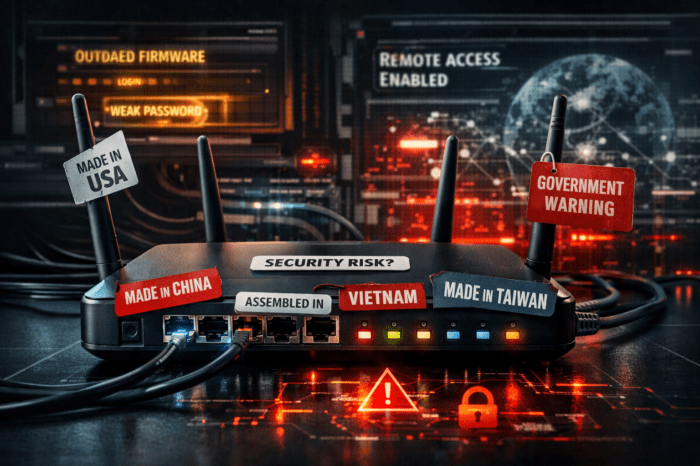
Routers: An Underestimated Entry Point
When people think about cyberattacks, routers — whether in a server room or a home office — rarely come to mind first. Yet these devices have been a preferred target for years: they are numerous, often poorly maintained, and sit directly at the boundary between the internal network and the open internet. The botnet KadNap, publicly documented on March 10, 2026, by the security research team Black Lotus Labs at US network provider Lumen Technologies, is perhaps the most instructive example yet of how systematically this weakness is being exploited.
The researchers have been tracking the network since August 2025. It now encompasses more than 14,000 compromised devices — primarily routers from Taiwanese manufacturer Asus, but also other edge devices, meaning network components that operate at the boundary between a local network and the internet. More than 60 percent of infected devices are located in the United States; additional infections have been detected in Taiwan, Hong Kong, Russia, the United Kingdom, Australia, Brazil, France, Italy, and Spain.
The Core Mechanism: Kademlia as a Cloak
What sets KadNap apart from other botnets is the way it conceals its own command channel. Classic botnets communicate via a centralized command-and-control server (C2) — a dedicated machine through which attackers direct their infected devices. Such servers can be located by security authorities, legally blocked, and shut down.
KadNap takes a different approach. The malware uses a modified version of the Kademlia protocol, an implementation of what is known as a Distributed Hash Table (DHT). This principle is well established in legitimate applications: BitTorrent, the Ethereum network, and other decentralized systems use Kademlia to distribute and locate information across a network of peers without a central server. A useful analogy: rather than calling a central directory for a phone number, you ask a chain of contacts — each one knows the next step, but no single contact knows the full answer. This makes the network resilient to outages and difficult to attack.
In the case of KadNap, this principle is used to conceal the IP addresses of the C2 servers. Infected devices use the DHT network to locate other infected nodes and work their way toward the command infrastructure — without defenders being able to easily identify and block the C2 addresses. Malicious traffic blends into normal P2P noise and evades conventional network monitoring.
However, KadNap’s own protocol implementation contains a structural weakness that Security Affairs has documented: infected devices consistently connect to the same two intermediate nodes before reaching the actual C2 servers. In a genuine decentralized Kademlia network, these nodes would change continuously. The consistency suggests that the attackers maintain persistent control nodes — and gives defenders a concrete point of attack to disrupt the network.
How the Infection Works
The attack begins with a shell script called aic.sh, downloaded from a C2 server onto the router. The script sets up a cron job — a scheduled task that restarts itself every hour at the 55-minute mark. It renames itself to .asusrouter, a filename deliberately chosen to resemble a legitimate Asus system process, then downloads an executable binary called kad. This fully integrates the device into the P2P botnet. The malware supports both ARM and MIPS processor architectures — two of the most widely used chip platforms in embedded devices such as routers.
The exact initial access vector — the specific vulnerability through which attackers first gain entry — has not been fully disclosed by Lumen. The Cloud Security Alliance notes in its analysis that in November 2025 — shortly before KadNap began spreading — two critical vulnerabilities in Asus routers were disclosed: CVE-2025-59366, an authentication bypass in the AiCloud feature with a CVSS score of 9.8, and CVE-2025-59367, an unauthenticated remote access flaw in certain DSL models. The accumulation of unpatched devices is likely to have contributed to KadNap’s rapid growth after its launch in August 2025.
The Business Model: Proxy as a Crime Service
Infected routers are not an end in themselves for the operators — they are inventory. Via a proxy service called Doppelgänger — accessible at doppelganger[.]shop — access to the hijacked devices is rented out to criminal customers. The service advertises proxy access in over 50 countries and claims to offer complete anonymity. According to Black Lotus Labs researchers, Doppelgänger is a rebranding of the earlier service Faceless, which in turn was associated with the TheMoon malware that has been active since 2014 — and which also targeted Asus routers.
Customers of the service use the hijacked home router IP addresses for DDoS attacks (distributed denial-of-service attacks targeting servers or networks), credential stuffing (automated login attempts using stolen credentials), and targeted exploitation campaigns. The decisive advantage for attackers: the malicious traffic originates from seemingly innocent residential IP addresses that appear on no blocklist.
Why IoT and Edge Devices Are the Preferred Target
KadNap is not an isolated case. In late 2025, the Kimwolf botnet compromised over two million Android-based TV boxes for the same purpose. The TheMoon malware, historically linked to Doppelgänger, has been active since 2014. The patterns repeat because the underlying causes remain unchanged: routers and other edge devices rarely receive regular firmware updates, frequently run on default credentials, and are often left untouched for years after initial setup.
For industrial IoT environments, the problem is even more acute. A compromised router in a fleet of connected field devices — for example, remote monitoring systems in energy supply or manufacturing — is not merely a security issue. It can impair the availability of critical systems, violate compliance requirements, and create liability exposure if the hijacked internet connection is used for criminal activity.
What to Do Now
No Asus statement specifically addressing KadNap has been published at the time of writing. The company issued a general security advisory in June 2025 in connection with earlier router attacks, recommending: update to the latest firmware, perform a factory reset, and set strong administrator passwords. That guidance remains valid.
Security researchers from Lumen, Black Lotus Labs, and other teams offer the following concrete recommendations:
- Update firmware immediately. Anyone who has missed recent updates closes known entry points. An update alone, however, does not remove an existing infection.
- Perform a factory reset if a compromise is suspected. A simple reboot is not sufficient — KadNap survives it via the cron job it installs.
- Disable AiCloud and remote management if these features are not actively in use. CVE-2025-59366 specifically affects AiCloud-enabled devices.
- Change default credentials. Many attacks of this type do not rely on zero-days — previously unknown vulnerabilities — but simply on factory passwords that were never changed.
- Replace end-of-life devices. Anyone operating a router that no longer receives firmware updates should replace it — regardless of KadNap.
- Monitor network traffic for P2P anomalies. Connections from within the network to public BitTorrent trackers can be an indicator of a KadNap infection.
Lumen has already blocked all connections to KadNap’s known control infrastructure on its own network and has announced that it will publish the Indicators of Compromise (IoCs) — technical signatures of the malware — in public feeds, enabling other network operators and security teams to follow suit.
Conclusion: A Familiar Weakness, A New Method
KadNap is technically sophisticated, but the underlying problem is familiar: devices that nobody maintains become infrastructure for attackers. What changes is the sophistication of the methods — decentralized protocols, originally developed for resilient P2P networks, are now being repurposed to conceal criminal command infrastructure. That makes takedowns by authorities and network operators considerably harder.
For developers and operators of connected systems, KadNap is a further reminder that security for edge devices is not a one-time project — it requires continuous attention. Deploying devices and then leaving them to their own devices will, sooner or later, deliver resources into someone else’s hands — without anyone noticing.