No VPN, no agent, no problem: IXT brings Zero Trust directly to the SIM card
VPNs were not designed for IoT and OT environments at scale – and their limitations become structural when thousands of headless devices are involved. – and the market is responding. Norwegian IoT specialist IXT shows, together with Zscaler, Illumio and Shift Security, what Zero Trust security at the SIM level can look like in practice.
The Key Points
- IXT integrates Zscaler Zero Trust Network Access (ZTNA) into its SecureNet platform, combining it with Illumio segmentation and Shift Security implementation into a bundled solution for cellular-connected IoT and OT devices.
- The core principle: every device connection is evaluated individually and restricted to the minimum required, rather than granting broad network access after a single authentication – no VPN infrastructure, no software agents on endpoints.
- Zero Trust for IoT is no longer a niche topic: alongside IXT and Zscaler, Netskope, Ericsson and others are working on comparable approaches, driven by growing pressure from the EU NIS2 Directive.
The VPN Problem: Trust as a Vulnerability
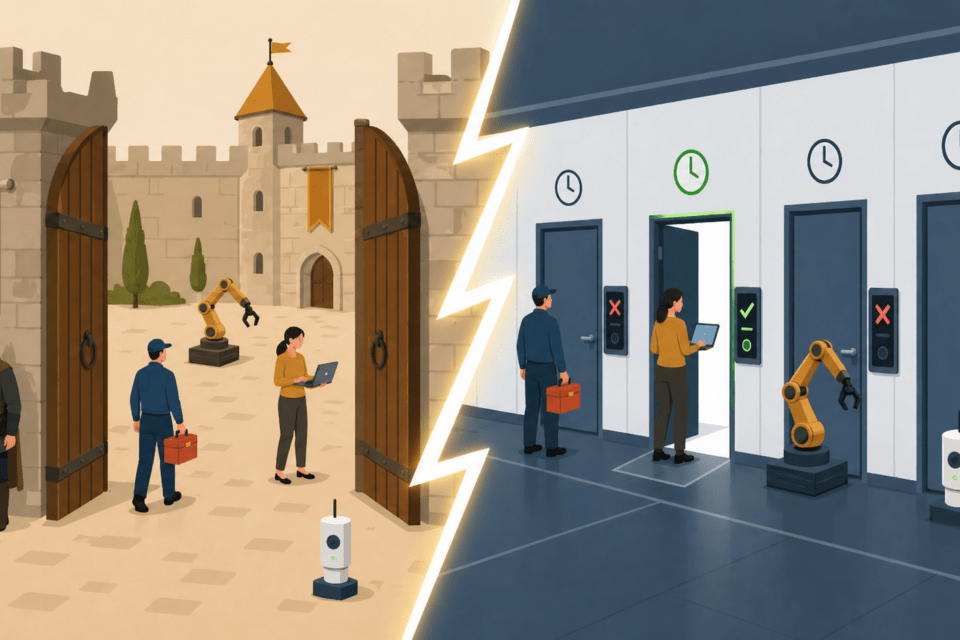
A device connects, provides the right credentials, and it’s in. What happens next, a classic VPN barely controls. That is the structural problem for industrial environments: a compromised device, a maintenance technician with overly broad access, a contractor with an outdated laptop – they all end up in the same network segment and can move around freely.
Henning Solberg, CTO and Co-Founder of IXT, puts it directly: “VPNs were designed to connect users on laptops to corporate networks. They were never built for thousands of headless devices in energy grids, water treatment plants and factory floors.”
The difference is not trivial. A laptop has an operating system on which a VPN client can be installed. A pump controller, a sensor in a pipeline or a meter in a power grid does not. These devices operate headless – without a user interface and without the ability to install additional software. Classical VPN architecture is simply not built for this world.
What Zero Trust Actually Means
Zero Trust Network Access, or ZTNA, inverts the trust principle. Instead of a single authentication at the network perimeter, every connection is evaluated individually: which device wants to communicate with which destination, at what point in time, and is that permitted under the applicable policy? Trust is not assumed – it is continuously verified.
In the IXT solution, this happens at an unusually deep level: directly in the SIM card. IXT operates as a so-called full MVNO – a virtual mobile network operator with its own core network – across more than 600 mobile networks in over 190 countries. All traffic from cellular-connected devices is routed through the Zscaler Zero Trust Exchange, where it is inspected and policy-enforced before reaching its destination. No exposed ports on the receiving end, no VPN tunnels, no software agent on the device.
This is the key difference from a Private APN – a private access point in the mobile network that isolates traffic, but makes no active judgement about what happens within that isolated space. Isolation is not the same as control. As IXT puts it: “A Private APN gives you isolation. Zero Trust gives you control and visibility on top of it.”
Four Functions, One Concrete Example
The integration covers four core functions. ZTNA restricts each device’s network access to the minimum required for its operation. Privileged Remote Access enables technicians and external contractors to access one specific machine through a browser-based portal, time-limited and fully recorded, with no VPN client distribution required. Dynamic Firewall Inspection checks all traffic in real time at the network edge. Malware and sandboxing functions scan file transfers and isolate suspicious content before delivery.
A practical example makes the difference tangible: a service technician from a maintenance firm needs access to a specific control unit. Instead of a VPN client granting access to an entire network segment, they authenticate through a web portal and land directly in front of the one machine they are responsible for. The session expires, the connection closes. No access to adjacent systems, no persistent credentials that need to be managed somewhere.
The Visibility Problem in Grown OT Environments
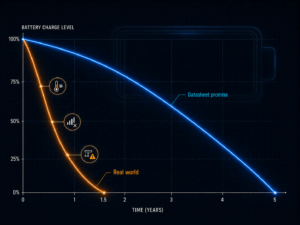
Zero Trust sounds like a clear concept. Implementation in practice is more complex – particularly in industrial environments that have grown over decades. Documentation is outdated, dependencies between systems are unclear, and nobody can say with certainty which device communicates with which.
This is where Illumio comes in, the third technical element of the solution alongside IXT and Zscaler. Illumio specialises in microsegmentation – the granular division of networks into small, controlled segments – and traffic mapping. In what is called learning mode, the system observes all real communication flows between devices, applications and systems over a defined period, without enforcing any policies. The result is a detailed map of actual connections.
From this foundation, Zero Trust policies can be developed that are grounded in real operational patterns rather than assumptions. Unnecessary or risky connections are identified and gradually eliminated. The approach is designed to make Zero Trust deployable in environments where a complete overview simply does not exist at the outset. Importantly, Zero Trust does not require complete policy definition upfront. Most operators start with visibility – mapping actual device communication flows – and define policies incrementally from there.
NIS2 as a Regulatory Driver – and a Growing Market
The EU’s NIS2 Directive, currently being transposed into national law across member states, significantly tightens cybersecurity requirements for operators of critical infrastructure. Among the notable changes: personal liability for board members and senior management in the event of non-compliance. Affected sectors include energy, water supply, industrial manufacturing and transport infrastructure.
IXT is not the only provider responding to this pressure. Zscaler launched “Zscaler Cellular” as a standalone product based on the same platform in July 2025, working with its own telecommunications partners. Netskope has extended its universal ZTNA solution to cover agentless IoT and OT devices. Ericsson and OneLayer have jointly introduced a Zero-Touch Zero Trust solution specifically for private mobile networks. The space is moving, and the underlying approaches share the same core principles.
What IXT brings to the table is the combination of its own MVNO core network, Zscaler traffic control, Illumio segmentation and the implementation expertise of Shift Security, a Norwegian specialist in Zero Trust architecture and secure network infrastructure. According to IXT, Zscaler is GDPR-compliant and personally identifiable data is stored within the EU.
Architecture, Not a Single Product
What this solution ultimately describes is less a finished product than an architecture: connectivity, traffic control, visibility and implementation as coordinated layers. Whether this bundled approach offers an advantage over direct offerings from individual vendors depends heavily on the specific environment.
For operators of critical infrastructure facing NIS2 pressure, without the resources or internal expertise to evaluate each component separately, such an integrated package may well be the pragmatic path forward.