5G: New standard, new risks
5G, the next mobile radio standard after UMTS (3G) and LTE (4G) is currently in the testing and introduction phase. Commercial introduction and use by 2020 is currently expected.
In addition to unforeseeable and hitherto unexplored risks for humans, animals and plants alike, 5G also carries old and new I(o)T security risks.
High speed – enormous transfer rates
According to current assessments and data from companies involved in the development of the new standard, 5G offers numerous advantages:
- up to 100x higher data rate than LTE networks (up to 10,000 Mbit/s)
- about 1000x higher capacity
- up to 100 billion mobile devices simultaneously worldwide
- extremely low latency; ping of less than 1 millisecond
- 1/1000 Energy consumption per transmitted bit
In practice, this would mean that the content of an entire DVD could reach the receiver via 5G within 3.x seconds – considerably faster than is currently possible with any conventional (A)DSL connection.
In order to achieve these high transmission rates and at the same time guarantee the stability of the signal, however, a considerable expansion of the underlying infrastructure is necessary. 5G transmits in the high frequency range.
The 5G signals on these frequencies have a much shorter range than signals from other transmission methods. In addition to the short range, buildings, plants and even raindrops can block and absorb the signal – this requires a significantly higher number of transmitting and receiving stations to reliably cover an area.
In the period from 2002 to 2015, the number of similar transmitting and receiving devices (antennas/masts) has already doubled. 5G will cause further – but exponential – growth of such plants.
This is also the point of criticism and warning calls from various researchers and institutes. It is assumed that permanent, area-wide irradiation by 5G (and comparable radiation sources) networks could not only lead to DNA damage, cause or promote cancer in humans – and also damage optic nerves and skin cells. Among other things, a connection is also postulated between the continuous expansion of such wireless transmission networks and the decline in the bee population.
Dangers also for the IoT
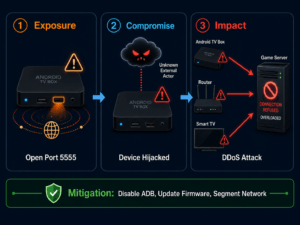
Even the predecessors of the current 5G procedure were susceptible to attacks. In 3G networks it was possible to hijack and hack SS7 (Signalling System 7), its mobile protocol; calls and data could be manipulated, diverted and intercepted. 4G/LTE should become more secure with the Diameter protocol – but still has old and new vulnerabilities that can not only enable targeted DDoS attacks, but also determine the location of a user/device, or intercept SMS messages and even query the IMSI.
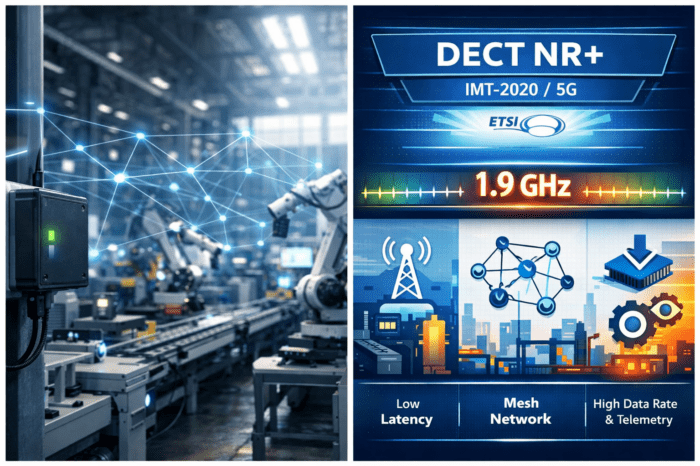
Backbone of the Internet of Things
5G, which is currently regarded as the “backbone of IoT/Industrial IoT“, should therefore meet the highest safety standards.
But not only the European Network and Information Security Agency (Enisa) fears that the new standard will not only have new weaknesses – it will also take over old ones. Trend Micro’s Forward Looking Threat Research Team (FTR) also believes that the Internet of Things and Industrial IoT will be most frequently and severely affected by various types of attacks – many of these attacks will be carried out over the new 5G network in the future.
The conversion to 5G will not lead to a complete renewal of the entire I(oT) technology for private or industrial users; the majority of users will simply insert the new technology into the existing structures – so that, for example, downgrade attacks would also make it vulnerable to many of the already known gaps from the predecessor protocols and communication methods.
In addition, old systems and structures are susceptible to a bandwidth for which they were not developed. Attacks from botnets over 5G with a capacity 1,000 times greater than before will be more effective than ever before.
Many of the potential targets will require individual radio communications. In order to be used for their actual purpose in IoT, they must have their own SIM card – and are therefore susceptible to the attacks mentioned above.
Heise also warns of new attacks by means of so-called “SIM-OTA SMS messages”, with which changes to the running system or even the download of malware to a compromised device could be triggered.
Against the background that SIM cards from German mobile phone providers have already been encrypted with 3DES and AES for many years, this scenario currently seems unlikely; because attacks of this kind have in the past mostly targeted old cards encrypted on the basis of Single DES.
Carriers would nevertheless require the use of a “SIM Inventory Management Platform” – an Equipment Identity Register (EIR) had also been mentioned. EIRs are rarely used in the telecommunications industry. Another possible approach would be a 5G platform, a “telecom security orchestrator”.
The development in and around the IoT undoubtedly remains exciting.