GandCrab: Threat from the Internet (of Things)
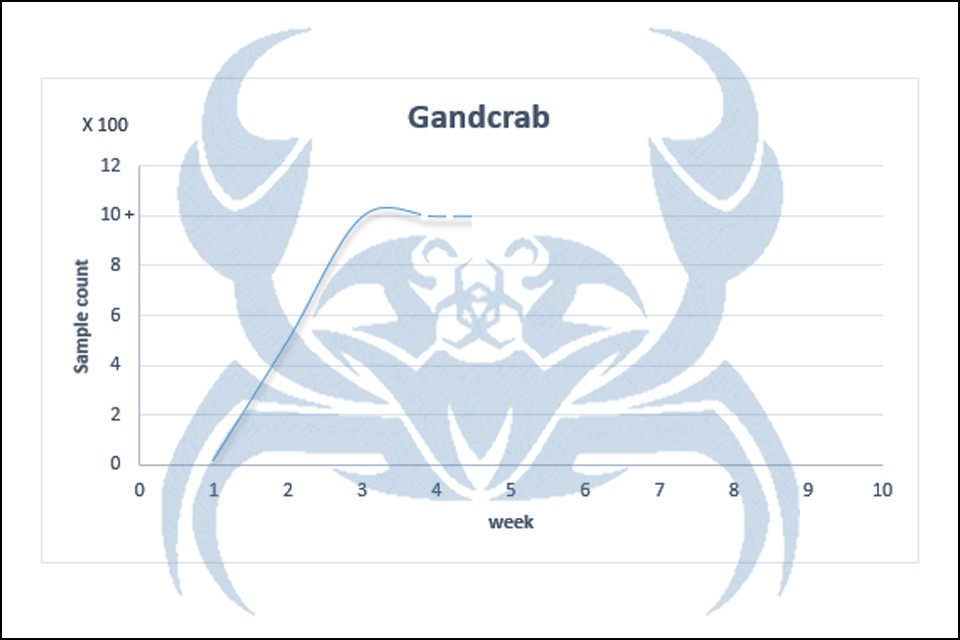
GandCrab, the Ransomware, is currently attracting renewed attention with a new wave of attacks.
The main targets of the attacks in the new scenario are the HR departments of small and medium-sized companies whose I(o)T structures and devices are not sufficiently protected against such attacks – and whose employees may not be sufficiently careful with emails and file attachments.
What is GandCrab?
GandCrab is a ransomware that has been in circulation in various versions since the beginning of 2018 – and is constantly being further developed by its “operators”.
(Ransomware is a type of malicious software from cryptovirology that threatens to publish the victim’s data or perpetually block access to it unless a ransom is paid. While some simple ransomware may lock the system in a way which is not difficult for a knowledgeable person to reverse, more advanced malware uses a technique called cryptoviral extortion, in which it encrypts the victim’s files, making them inaccessible, and demands a ransom payment to decrypt them – Source: Wikipedia)
The first early versions of GandCrab were still aimed at individuals – such as users of P2P networks and players who downloaded and executed individual files (such as an alleged piece of music; a trainer or a NoCD crack for a game) for a specific purpose from public servers without verification.
Networkable ransomware
Versions 1 and 2 of GandCrab only searched on the infected computer for files and drives to encrypt and force the owner to pay a ransom for the datas decryption. In the second quarter of 2018, the 3rd version of Ransomware was “released” – it was now also able to access and encrypt network resources and drives.
Beware of file attachments with email applications!
The 5th (or even higher) version of GandCrab is currently in circulation. At present, nothing is known about their potentially increased malicious potential – various IT security and anti-virus companies are analyzing the new variant.
You and your system(s) can only become infected if you execute a file attachment that is sent to you by email on the pretext of applying for a supposedly vacant position.
Although a large number of common (including free) virus and malware scanners already recognize GandCrab, the most secure protection against such ransomswares is and remains common sense. The email letters of the Ransomwares are, since they are sent in bulk, mostly generic and refer to a possibly not advertised position. In addition, it is absolutely unusual to attach an executable file to an application.
Currently there is no decryption tool available to break the new encryption of GandCrab! A very careful handling of incoming mails and possible file attachments is recommended besides the use of reliable virus and malware scanners.