IoT Botnets Mirai & Gafgyt attack again
A few days ago “Unit 42”, the cyber security team of the Californian network and enterprise security specialist Palo Alto Networks, discovered new variants of the well-known IoT botnets Mirai and Gafgyt.
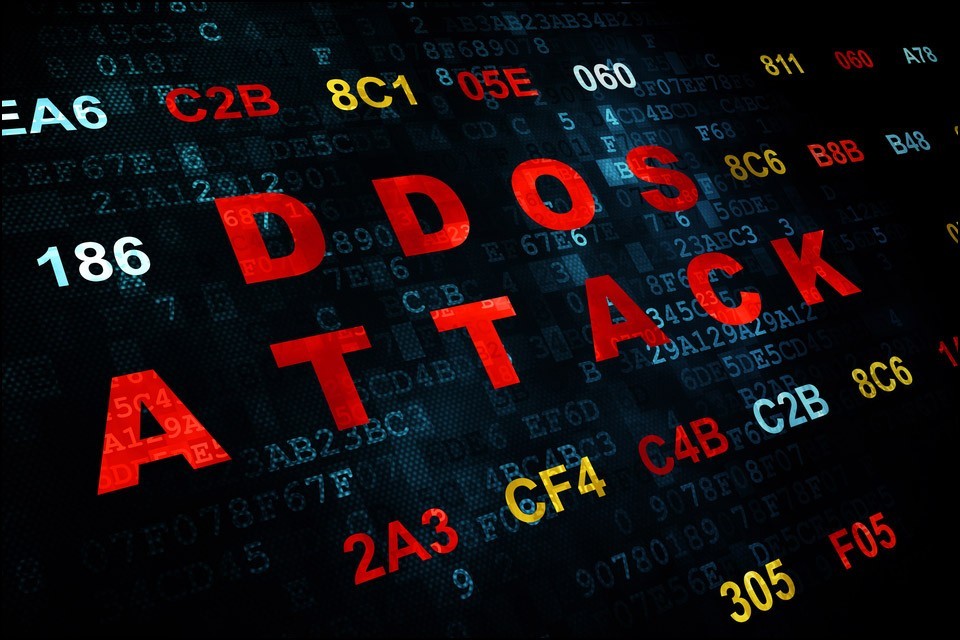
Mirai, a Linux malware, is suitable for hijacking IoT devices and using them for DDoS attacks (In computing, a denial-of-service attack [DoS attack] is a cyber-attack in which the perpetrator seeks to make a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connected to the Internet. Denial of service is typically accomplished by flooding the targeted machine or resource with superfluous requests in an attempt to overload systems and prevent some or all legitimate requests from being fulfilled. – Source: Wikipedia) to abuse.
Gafgyt, another Trojan (also known as Bashdoor or BASHLITE), is also targeting Linux systems on the Internet of Things and is also used to perform DDoS attacks on other systems.
Both botnets have been connected since the end of November 2016 to countless attacks on IT and IoT structures all over the world.
Mirai attacks new exploits
The recently discovered new Miari variant seems to attack 16 different vulnerabilities in Apache Struts.
(Apache Struts is an open-source web application framework for developing Java EE web applications. It uses and extends the Java Servlet API to encourage developers to adopt a model–view–controller (MVC) architecture. – Source: Wikipedia)
The exploit was set at CVE-2017-5638, a common vulnerability in command execution via self-created Content-Type, Content-Disposition, or Content-Length HTTP headers.
Gafgyt attacks SonicWall
While locating the new Miari variant, “Unit 42” – the cyber security team of Californian network and enterprise security specialist Palo Alto Networks – also discovered a previously unknown variant of Gafgyt that attacks vulnerabilities in SonicWall’s Global Management System (GMS).
The integration of exploits targeting Apache Struts and SonicWall is seen as an indication that these IoT/Linux botnets are shifting from consumer devices to enterprise targets! All companies should therefore ensure that they not only keep their systems up to date, but also their IoT devices.