Cryptomining: The latest threat to IoT

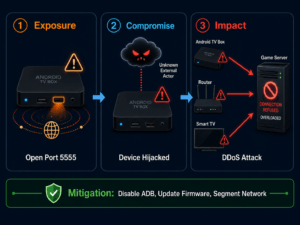
While the use of hacked or malware-infected IoT devices and networks was mostly limited to using the acquired devices as cyberweapons in order to execute massive DDoS (Distributed Denial of Service) attacks in the past, other threats to IoT devices are now surfacing. The most remarkable – and potentially most dangerous – of them at the moment: Cryptomining.
This threat infects vulnerable IoT devices, from building sensors, security cameras, televisions, refrigerators to mobile phones with malware that accumulates bits of a digital currency in the background – the so-called “mining”.
Cryptomining – Attack on IoT devices
Mining is a process of verifying transactions in a crypto currency network by solving complex mathematical problems with powerful computers. “Bitcoin”, currently probably the most popular digital currency, is very difficult to win without having access to a supercomputer or a mining cluster – but another cryptocurrency called “Monero” can be mined with a network of IoT devices.
At the Mobile World Congress, Internet security and anti-virus software manufacturer Avast demonstrated the process by creating a network of hijacked devices to mine for “Monero“. For this purpose, interested trade fair visitors infected their equipment voluntarily with the necessary software – but at the same time, Avast also provided data on the potentially usable, vulnerable equipment in the vicinity of the event location. Queries using the IoT search engine “Shodan. io” showed that more than 58,000 IoT devices in Barcelona alone were open or vulnerable to infection with cryptominingmalware.
The advantage for the attacker is obvious – the damage for owners and operators of infected devices can be high. Mining software uses the highest possible computing power of a device. While every commercially available PC can register and inform the user of the enormous increase in energy consumption and thus also heat generation via its own sensors, very few IoT devices have the corresponding on-board equipment – and not even the active cooling mechanisms of personal computers. Correspondingly, overloading and overheating can lead not only to an enormous slowdown of affected IoT devices but also to their total loss.
Cryptoming-malware has recently appeared increasingly on major distribution platforms such as Google Play – so the potential risks are enormous. The most effective protection against these malwares is as old as malware itself. Do not run any unknown programs; do not install any software from unknown sources and make sure that the manufacturer/editor certifies and distributes any allegedly necessary updates. In addition, you can also protect your devices using appropriate software.