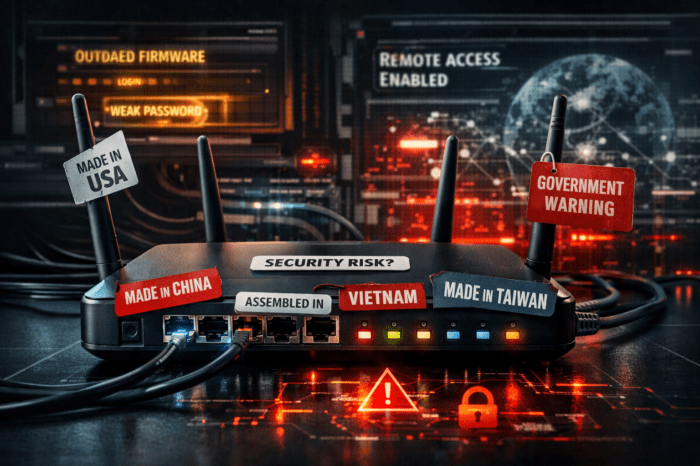
VPN Filter threatens more devices than expected

The router malware VPN filter threatens more devices than expected. And: Not only network devices, but also endpoints could be infected.
Security researchers from Cisco Talos published new findings on router malware VPN filters on Thursday. A Stage 3 module called “ssler” extends the danger beyond the network device to the devices that are connected to the router in question. If the malware succeeds in infecting these endpoints, the entire network is considered infiltrated. In addition, security researchers discovered an extension of the “kill” command, which erases the traces of malware and makes devices unusable.
Until recently, devices of the manufacturers Netgear, TP-Link, Linksys and Mikrotik, which are primarily used by private users, the self-employed and small companies, were considered to be particularly affected. Cisco Talos now explained that routers from ASUS, D-Link, Huawei, Ubiquiti, UPVEL, and ZTE could also be infected. Cisco Talos released a new overview of all endangered device types (see table).
VPN Filter - Affected Devices
| Manufacturer | Device |
|---|---|
| ASUS DEVICES | RT-AC66U (new) RT-N10 (new) RT-N10E (new) RT-N10U (new) RT-N56U (new) RT-N66U (new) |
| D-LINK DEVICES | DES-1210-08P (new) DIR-300 (new) DIR-300A (new) DSR-250N (new) DSR-500N (new) DSR-1000 (new) DSR-1000N (new) |
| LINKSYS DEVICES | E1200 E2500 E3000 (new) E3200 (new) E4200 (new) RV082 (new) WRVS4400N |
| MIKROTIK DEVICES | CCR1009 (new) CCR1016 CCR1036 CCR1072 CRS109 (new) CRS112 (new) CRS125 (new) RB411 (new) RB450 (new) RB750 (new) RB911 (new) RB921 (new) RB941 (new) RB951 (new) RB952 (new) RB960 (new) RB962 (new) RB1100 (new) RB1200 (new) RB2011 (new) RB3011 (new) RB Groove (new) RB Omnitik (new) STX5 (new) |
| NETGEAR DEVICES | DG834 (new) DGN1000 (new) DGN2200 DGN3500 (new) FVS318N (new) MBRN3000 (new) R6400 R7000 R8000 WNR1000 WNR2000 WNR2200 (new) WNR4000 (new) WNDR3700 (new) WNDR4000 (new) WNDR4300 (new) WNDR4300-TN (new) UTM50 (new) |
| QNAP DEVICES | TS251 TS439 Pro Other QNAP NAS devices running QTS software |
| TP-LINK DEVICES | R600VPN TL-WR741ND (new) TL-WR841N (new) |
| UBIQUITI DEVICES | NSM2 (new) PBE M5 (new) |
| ZTE DEVICES | ZXHN H108N (new) |
| UPVEL DEVICES | Unknown Models (new) |
| HUAWEI DEVICES | HG8245 (new) |
Manufacturers give recommendations to deal with VPN Filter
However, some manufacturers provide information on how to deal with the security problem. D-Link and Netgear, for example, assume that they can close the gap with firmware variants already available and recommend installing the latest firmware version. TP-Link advises users of its devices to change the factory-set values for the administrator user and to disable remote management functions if not needed.
FBI: Limited danger after restart
As reported, Cisco Talos suspects state actors behind VPN Filter and suggests in the context a responsibility of the Russian government – or the Russian secret service. After the attack on about 500,000 network devices became known, the FBI had managed to contain the danger. The American security authority has gained control over the server through which the malware obtains information for reinstallation if it has been partially removed. If you now restart an infected device, the malware will not get rid of it, but it will only connect to one side of the FBI, which can identify infected devices in this way. However, this does not necessarily mean that the malware will remain harmless in the long term, as the US Department of Justice explains.