IoT security: Leaked logins – the carelessness is baffling

Researcher Ankit Anubhav, specialized in IoT security, recently drew attention on a list circling the internet. It contained thousands of IP addresses of IoT devices including their login data. Many of the devices are still accessible via Telnet, some of them already have been taken over by botnets. What baffles is that despite the many incidents related to poorly secured IoT devices and constant warnings from security professionals, most of the logins couldn’t been easier to guess: When “admin:admin” or “root:123456” grants access to a device, calling it “hacking” to take control already sounds like an insult. My plea: Think of security first, when you think of the IoT!
While the list with the devices was public since June, it has now been taken offline from its original source. It’s available on other sites, but we won’t mention them here. Science researcher and former McAfee employee Ankit Anubhav made the incident public on twitter, since then the story surfaced and the list went offline quickly. But for thousands of devices it’s already too late. Some had been captured by botnets: a new passport “GMB182” typically given by botnet malware indicates that.
33000+ telnet credentials of IoT devices exposed on pastebin.
Link : https://t.co/v5uGw4Llsv #iot #hacking #malware #infosec @newskysecurity pic.twitter.com/0Lg7q8G0Kq— Ankit Anubhav (@ankit_anubhav) 24. August 2017
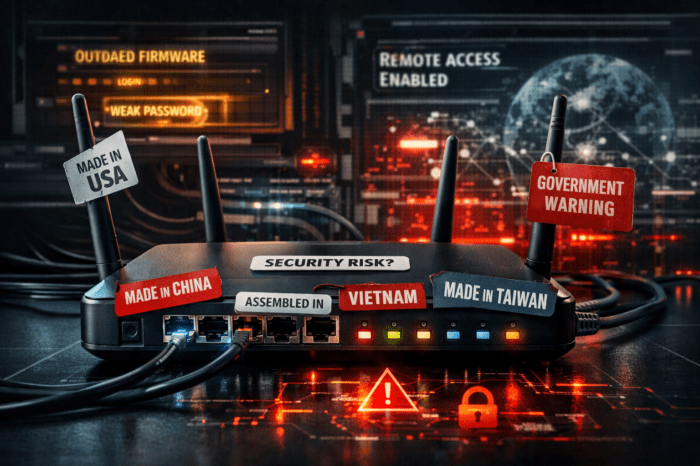
What’s baffling is the carelessness users and probably also hardware vendors display, when a.) vendors deliver hardware with too easy to guess standard passwords and b.) users do not change those passwords after putting their devices into service. It should be in everyone’s own interest to prevent third parties from taking control over their devices and probably spying on them so easily.
IoT security always should come first
But then again, it’s not “just” about protecting one’s own personal interests, but also protecting the rest of the internet: If a device is accessible publicly, it’s easy to hijack and then being used in organized botnets as a weapon to attack other systems and cause damage on a much greater scale. All with the help of the thousands of poorly protected devices.
Hardware manufactures urgently need to find a way to master the thin line between an easy installation process of a device and, at the same time, protecting their clients’ security interests without expecting them to be experts in that field. At least a few minimum standards of device security should be made obligatory before a device is allowed to be sold.
You might also like to read: