If Skynet awakes, it probably hits you in the car wash first

A serious security issue relating fully automated car washes made the headlines this week: Researches found a way to manipulate internet-connected drive-through car washes that could physically attack vehicles and their passengers. The problem: configuration of the machines could be changed online. A decentralized system could have avoided that.
Remember Judgement Day? That day the artificial network “Skynet” became self-aware and turned the machines against humanity? Well, it might not be as worse as in the sci-fi movie Terminator, but still, the billions of unsecure devices in the Internet of Things pose serious security threats. And this one could literally punch you in the face.
According to a recent motherboard report, the vulnerability affects a system called “PDQ LaserWash”, a fully-automated and touchless car wash system, popular in the US. Instead of brushes, a mechanical arm moves around the car inside the washing box and sprays it with water and wax. Attendants are not required to operate the machine. Bay doors at the entrance and exit automatically close during the operation.
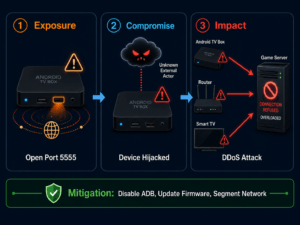
Via the popular search engine for IoT Devices “Shodan.io”, the researches could identify over 150 of these washing systems still connected to the internet. The report further claims, that with a self-written attack script, they were able to bypass the simple authentication mechanism, render the infrared collision sensors of the mechanical arm useless and re-program the station to keep passengers locked inside and have the mechanical arm attack the car and spray water on potentially fleeing passengers.
While the vulnerability itself is not new and had already been discussed a few years ago, it could now been tested for the first time in a real life situation in cooperation with a car wash owner in Washington. According to motherboard, the researchers filmed the test but were not given permission to publish the video of the actual hack itself.
Edge computing: decentralized IoT ecosystems are safer by design
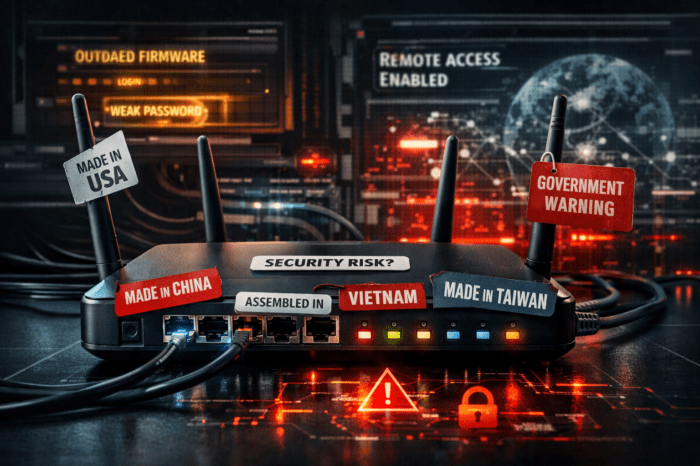
This is just one of many examples showing weaknesses in IoT installations with a centralized architecture, allowing intruders to remotely change the behavior of the installation at any time. In this case and because of the nature of the connected machines, they could be programmed to physically attack and harm people.
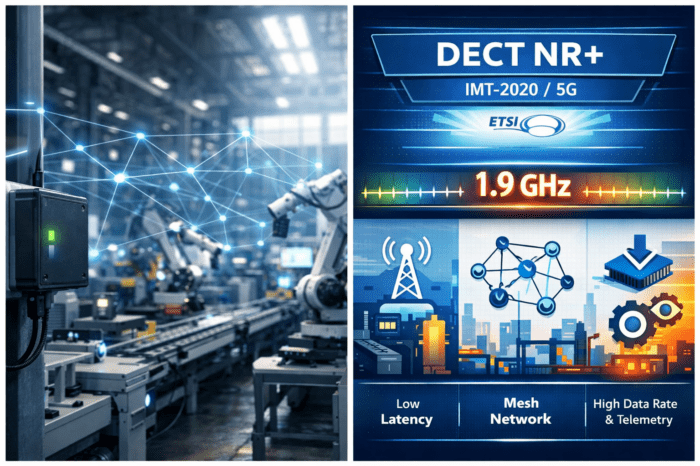
Instead of handing over complete control to a centralized unit, a more edge-orientated approach could increase security significantly: Use devices that are able to exchange their statuses directly with each other, and, once configured, could be disconnect from any configuration software or even from any central controller and work autonomously.
This approach is called “edge computing” where the necessary processing tasks are handled by the devices at the edge of a network. The data for analysis or monitoring purposes could still be send to an external server. The possibility of unwanted manipulation would be reduced drastically.
In this actual case, access to the configuration server without any firewall and simple standard passwords made the system even easier to hijack.