Digitization, the big challenge for IT security

While researching this article, I realized that digitization and the commonly used term IoT, currently on everyone’s lips, is used in a variety of ways, actually just the umbrella term for a change in our society, in which everything – both in private and in the corporate sector – things are becoming faster and more closely networked, without being aware of the effects on society and safety.
We should actually take a closer look at the term “digital transformation,” because this transformation will mainly be going through companies in ever faster cycles over the next few decades. Comparable is the digital transformation with industrialization in the 19th century. No one could predict the impact on society and companies during this time.
If I want to push a new company for IoT into the market, I can only gain my market position through quick development, strong marketing and sales, but not through IT security
When I look at the IT security landscape with its problems today, I get deeply scared. Because already today companies are suffering:
- Shortage of skilled labour in IT security
- Information overload caused by the log files generated by IT security assets
- Poorly tuned and maintained SIEM’s (Security Incident and Event Management Tools)
- Lack of awareness among employees and management
- Attackers who slip through covered/camouflaged by the masses of events
- Patch orgies by the software vendors to get their ever-new security problems under control
- Attackers who develop better and more sophisticated attacks
- Increasingly complex tasks for the IT departments
- Blind spots on Social Engineering used by attackers
- Profit and revenue over Security needs
But how should companies compete in the field of IT security (if they can not already do so today), when the digital transformation exponentially increases the number of systems and applications. Furthermore, the complexity will increase with the more frequent mixing of systems and transport medias (wired, wireless on new frequencies), the variations of which feel like they are approaching a near-infinite number.
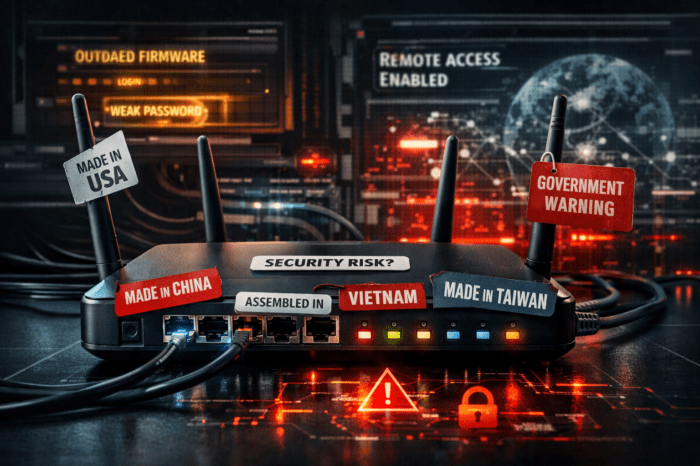
If I want to push a new company for IoT into the market, I can only gain my market position through quick development, strong marketing and sales, but not through IT security in my product. In 2016 alone at DEF CON 2016, hackers found 47 vulnerabilities in 23 IoT devices. IoT is part of the digital transformation and so it is quite conceivable that a compromised cooler shelf in a supermarket is the springboard with which an attacker paralyzes the whole logistics of a supermarket chain.
Utopia? I think no, just enter “IoT hacks” or “IoT Vulnerabilities” into Google and see what’s possible today.
Smart home? Certainly companies will use many devices in the future to save energy and control “smart”. But as they are constructed without Security in mind, they are often attackable. You will certainly dislike at 30 ° C outside temperature when – by a harmless attack on the heating system – the heating in your office kicks in.
Enough of Pessimism, how can one adjust oneself from the IT security view to the digital transformation?
We have to make our SOCs and IT security departments leaner from a technical point of view, and agile from Incident Response’s point of view. That also means that we may have to have a multi-layered setup (Separate IT-Security Departments for Commercial-IT, Process-IT, IoT), which orchestrates the overall IT-Security and work closely together.
This also means first to stop the information overload on all levels. I know companies that have to monitor nowadays 1.6 billion (!) events per day. With digitization and the wide use of IoT these numbers will increase dramatically and our ability to respond will drop the same way.
As a consequence, the view on IT security must be changed – namely the view from perimeter security to the view of the attacker. What does he want, which attack-vectors and techniques does he use? We have to get rid of the noise and the false positives in out IT-Security control assets, by looking more on the targets of an attacker, less on the outer fence.
With digitization and the use of IoT, we have to change now. It is not on the horizon anymore, it is reality.